Cellphones, like many digital devices, can be hijacked. It happened to Jack Dorsey, CEO of Twitter, other celebrates, and many ordinary people. So how does cellphone hacking happen and, more importantly, how do you protect yourself from an attack?
The Subscriber Identity Module (SIM) inside a smartphone is used to uniquely identify its owner. A mobile phone service provider uses the SIM, among other things, to seamlessly port a telephone number to a new device. This feature is, normally, used when someone lost a phone, had it stolen, or when they are switching services to a new phone.
Scams start with criminals gathering personal details about the victim – usually the result of phishing or spear phishing attacks – buying them on the dark web or gathering the information from acquaintances. Once the criminal has obtained enough personal information, they then contact the victim's mobile telephone provider and convince them to port the victim's phone number to their SIM. For example, they might impersonate the victim by using personal details to appear authentic or claiming that they’ve lost their phone. In some countries, the mobile service operator will approve the SIM swap by just pressing “1” in the automated application.
Once this happens, the victim's phone will lose connection to the network, and the criminal will receive all the SMS and voice calls intended for the victim. This allows the criminal to intercept any one-time passwords sent via text or telephone calls to the victim, thus circumventing security features of accounts (bank accounts, social media accounts, etc.) that rely on text messages or telephone calls for authentication.
The U.S. Department of Homeland Security is recommending that government agencies and enterprises stop using SMS for sensitive communication. SMS can be exploited by criminals and nation-state actors. SMS isn’t encrypted, and there are other ways to gleam SMS messages besides SIM swapping, including bribed telephone employees and government agencies who monitor communications.
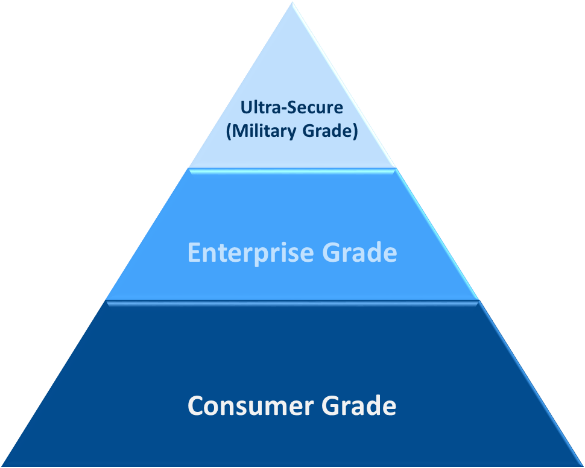
Enterprise Unified Communication and Collaboration (UC&C) applications don’t have Military Grade security built into them. Enterprises and government agencies should provide additional security capabilities for the UC&C workstreams that need ultra-security. One use case is providing an ultra-secure out of band communication channel in the event of a cyber-security breach. There is no sense in having the cyber-criminals listening in on the remediation plans.