According to Metrigy’s Workplace Collaboration: 2021-22 global study of 476 organizations, almost 68% have deployed team apps, while more than 57% of participants view team apps as a hub for work—integrating data and applications into contextual workspaces. Compared to email, team applications provide significant and measurable improvements in productivity and responsiveness. It’s no wonder that almost 54% of companies now use, or plan to use, team collaboration apps to support business-to-business and business-to-consumer collaboration.
The last several weeks have seen numerous high-profile team collaboration security concerns. As collaboration security vendor
Safeguard Cyber noted in a recent
blog post, hackers compromised EA Games’ Slack instance using a combination of a stolen cookie and a social engineering attack to reset a password. Slack isn’t alone as a potential vector of attack as security researchers at the security firm
Tenable also discovered a potential zero-day vulnerability in Microsoft Teams that could have allowed an attacker to compromise user accounts. These types of software vulnerabilities aren’t new—vendors routinely issue patches for discovered and reported security flaws—but they do underscore the need for those responsible for collaboration security to ensure that they’re taking a proactive approach to vulnerability awareness and protection, and patch management.
Our data shows that most companies do not yet have a proactive workplace collaboration security plan. Among our study participants, just 41% have such a plan today, though an additional 22% are developing one. Even among those with a plan, we find two challenges that can lead to a higher level of risk:
- Most security plans are still voice-centric and perimeter-based
- Chief Information Security Officer (CISO)/Chief Security Officer (CSO) organizations may not adequately understand and prioritize against potential risk
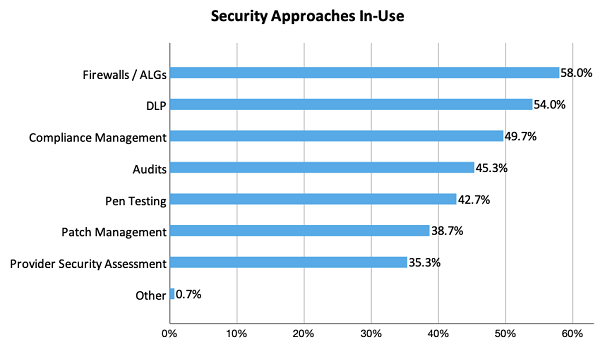
Among those with a workplace collaboration security plan, the biggest component is perimeter-based security, such as firewalls and application-layer gateways (ALGs) to protect internal applications and data from external attacks (see graphic above). With the typical network perimeter increasingly dissolving as employees access apps from various devices at home—and expand their use of cloud apps—the old “crustacean” network security model that uses a hard-exterior shell to protect a soft mushy interior is no longer acceptable.
Instead, companies must move toward implementing a zero-trust security model that treats all users and devices as untrusted, and then once authenticated, only allows access to permissible services. Zero-trust models may even extend to application service providers through end-to-end encryption, meaning that application providers are unable to see customer data unless specifically granted permission by the customer.
We also discovered that in just over 50% of companies, the CISO/CSO team owns responsibility for collaboration security. However, in those organizations with the highest measured success for their collaboration investments (in terms of increased revenue, cost savings, or productivity improvements), collaboration teams are more likely to own the security of collaboration apps. This data implies that CISO/CSO teams may lack expertise and understanding of the risk that collaboration applications present if not properly secured. The more high-profile attacks, like that against EA Games, should change this dynamic, but it’s imperative that CISO/CSO teams bring collaboration application expertise into their domains and increase their focus on collaboration security threats.
Finally, companies should consider investing in collaboration security tools to standardize on policy enforcement across multiple apps, and to proactively enable protection against phishing and other social engineering attacks. Tools from vendors such as Safeguard Cyber, Theta Lake, and Unify Square provide the ability to ensure consistent policy configuration and compliance. Additionally, companies should take advantage of advanced security capabilities available from their collaboration vendors to protect against data loss. Examples include Cisco’s Cloudlock cloud access security broker (CASB) as well as security capabilities offered by Google and Microsoft for their collaboration suites. Consider utilizing enterprise key management to gain control over your encryption keys, and using end-to-end encryption where necessary for the highest level of application security.
The EA Games breach is unlikely to be the last attack that leverages team collaboration apps. A proactive security approach based on Zero-trust that’s specifically applied to collaboration applications and implemented and managed through security policy and enforcement controls is your best route to preventing an attack.