In
part one of this series, we described three foundational functions that NSA recommends to reduce cyber security attacks: Multi-Factor Authentication, Role-Based Access, and Application Whitelisting. Upon this foundation, we at NetCraftsmen recommend three additional functions: network segmentation, operating system patching, and backups,
described in part two of this series.
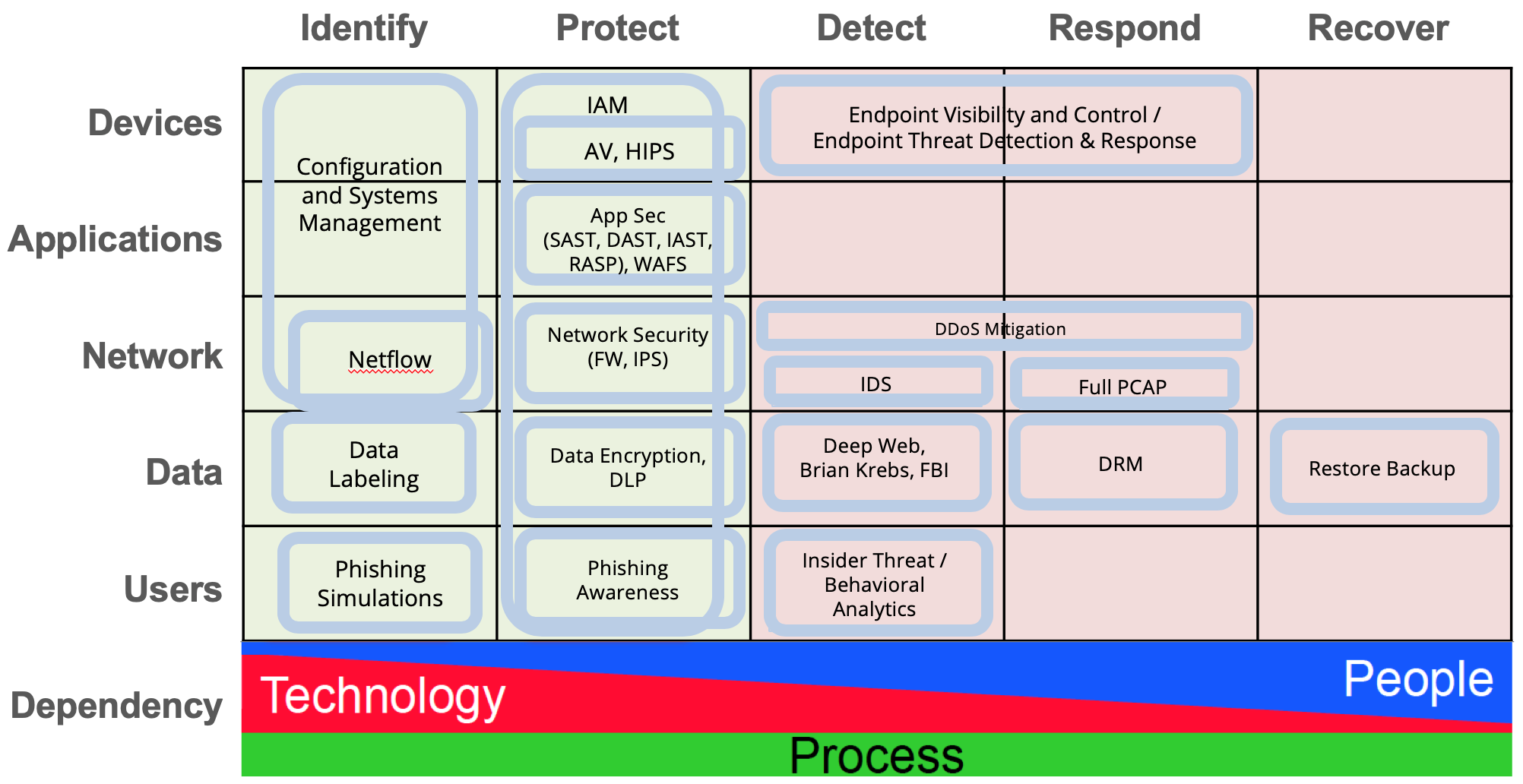
The Cyber Defense Matrix
The “Dependency” section at the bottom of the grid shows the mix of people, process, and technology that are required for each of the five operational functions. Automated technology is used to a greater extent in the functions to the left, while people are more important in the functions to the right.
The “Identify” and “Protect” functions, colored light green on the left, are used prior to a security event and the three remaining functions, highlighted in light red, are used after a security event. So, Identify and Protect are functions that protect the IT systems from attacks, while “Detect, Respond,” and “Recover” are functions related to handling a security event that has occurred.
Each intersection within the matrix identifies a security mechanism that applies that column’s function to the corresponding asset of that row. The intersections that have no mechanism are blank. A mix of people, process, and technology are needed to implement each mechanism. For example, Netflow provides the “Identify” function for “Network” assets, because it identifies conversations between network endpoints. The process for using Netflow would use technology to identify network traffic flows that are of interest. Those flows would be investigated further by the security team.
Using the CDM
Each mechanism in the CDM can be colored to show whether it’s purchased, fully implemented, or staffed (including staff training):
- Red: Not implemented
- Yellow: Purchased but not implemented
- Blue: Purchased and implemented but staffed and not fully operational
- Green: Fully operational
The colors allow you to quickly identify holes or duplication in your security systems. Adding budget information for CapEx and OpEx spending allows you to see how your security budget is being used (see
Security Budget Analysis with CDM). You may find that most of your budget is going into the “Detect” function, while “Protect” is under-supported. As with any endeavor, it’s always better and less costly to implement preventive functions than to use remedial functions.
Additional Steps
The CDM is a useful tool to identify mechanisms that should be on your list of next steps. Not all mechanisms have the same return on investment. For example, so-called spear-phishing campaigns are becoming more prevalent. Improving phishing awareness with simulations and education could easily be much more effective in reducing security events than spending a lot of money on detection tools.
At NetCraftsmen, we recommend the following CDM mechanisms for implementation on top of the foundational functions:
- Conduct phishing awareness campaigns. Teach everyone how to recognize malware attempts and avoid clicking on joke links. Awareness campaigns can significantly reduce the number of malware intrusions. Just know that it’s unlikely to eliminate this as a source of malware. It’s just too easy to construct convincing emails that lead to clicking on a link that loads malware.
- Use a DNS (Domain Name System) validation service. Prevent command and control connections that malware uses to contact its control systems. This is because DNS names are frequently used by malware to easily move their control infrastructure and avoid static blocking techniques.
- Install security scanning and remediation systems. Scan end systems for malware and when found, isolate those systems until remediation can be performed. The remediation process should be as automated as possible.
Defense in Depth
Good IT security relies on defense in depth, which means that multiple systems are used to prevent, detect, and remediate attacks. The mechanisms in the CDM work together to provide comprehensive IT security measures. Ultimately, a network security strategy should be built on a solid IT foundation, and additional mechanisms can be added as needed when the budget allows.